Video Surveillance as Part of Airport Security
| Anybody who traveled by plane at least once knows that airport security is tight. Of course, it’s not unreasonable to have such security in a place prone to being crowded all the time. In order to have perfect control over any situation, this security has to be rather sophisticated. This, in turn, makes video surveillance equipment an essential and irreplaceable part of it. The sheer size of the facility usually renders cameras invisible to a naked eye but they still tirelessly do their work. Let us take a closer look at what that work actually involves. |
|
|
|
The very first and possibly the most important of their functions is counter-terrorism. The terrorists are notorious for targeting airports, as such active public places tend to attract a lot of attention. It is a common misconception that the first part of security that looks for potential terrorists is metal detectors and luggage examination. Actually, the first line of anti-terror defense consists of video surveillance equipment. Modern software with intellectual properties (such as face recognition) enables cameras to scan the crowd for suspicious activities or individuals. They can analyze both faces and behavioral patterns to detect potential threats before something happens. Moreover, such features as cloud storage enable multiple airports to share what cameras see among a great number of operators. This makes security even more efficient as chances of human error diminish and location of specific faces (e.g. those on watch lists) is simplified. |
| Another important part of airport security is constantly maintaining order. Public places can become incredibly chaotic in a matter of minutes, unless preventive measures are taken without delay. Needless to say, airports are no exception. Video surveillance equipment helps finding sources of disturbances so that they can be quickly neutralized by dispatching a security guard. Cameras also make sure that certain areas of the airport are accessed only by the authorized personnel. Finally, cameras can detect objects that stay at a certain place unattended for too long. Be it a bag, a packet or a car in the parking lot – it will be noticed and analyzed. This helps with both finding lost property and defending against terrorism. |
|
That’s a lot of work, isn’t it? Can Xeoma handle all this? Certainly. Let us test Xeoma’s features against these conditions.
- Counter-terrorism. Put the “Face Detector” module in the chain for the cameras that overlook entrances and exits. If you already have some photos from a watch list, you can train Xeoma to recognize those faces. To do that, use the module “File Reading” as a source and connect the “Face Detector” to it. Put the path to the photo (make sure that it is a JPEG-file) to the former’s settings. Now access the settings for the latter and put the person’s name in the Name of the person to recognize field. After that press the Train person recognition button. Now, if you choose React only to selected faces, you will see the name you’ve entered down below.
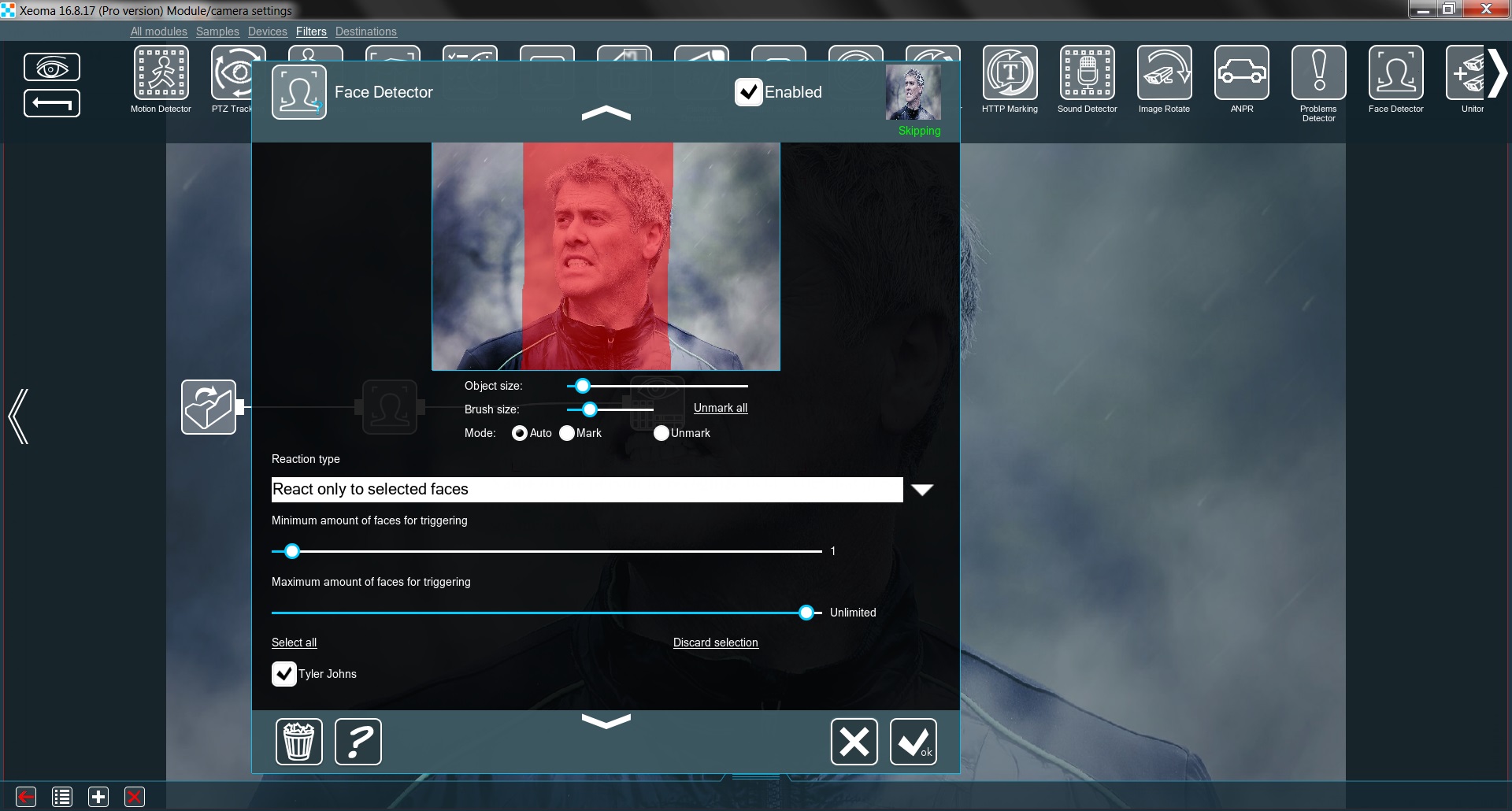
Now this faces can be recognized later. Do it for every photo and you are all set.
- Maintaining order. When it comes to monitoring areas that should be accessed only by the authorized personnel, you can also use the “Face Detector” (with all the personnel already accounted for) and set it to React to unknown or unselected faces. You can connect the module to “Sound Alarm” and/or “SMS Sending” to warn the authorities about the trespassing. Add “Preview and archive” to know exactly what cameras detected.
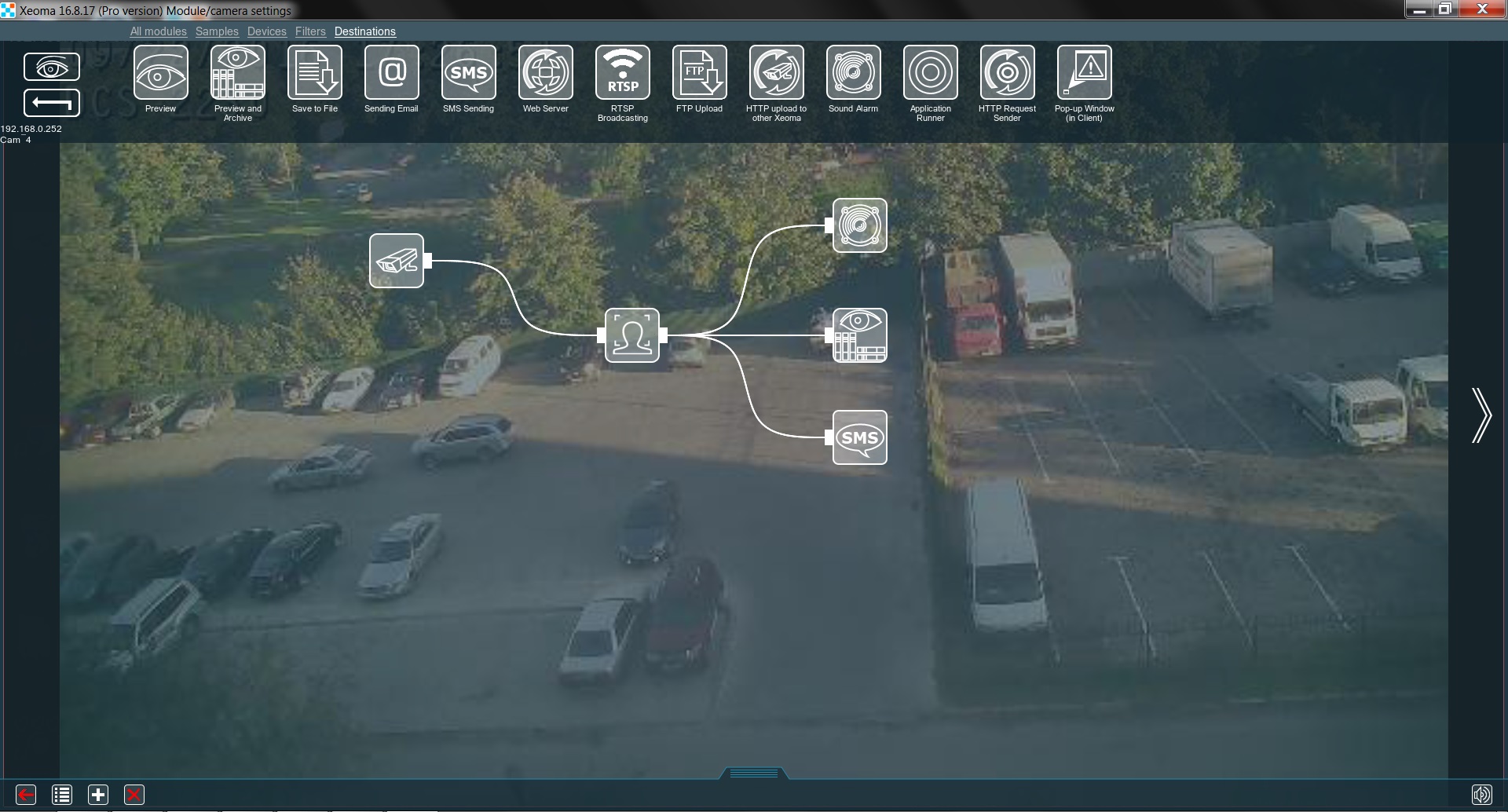
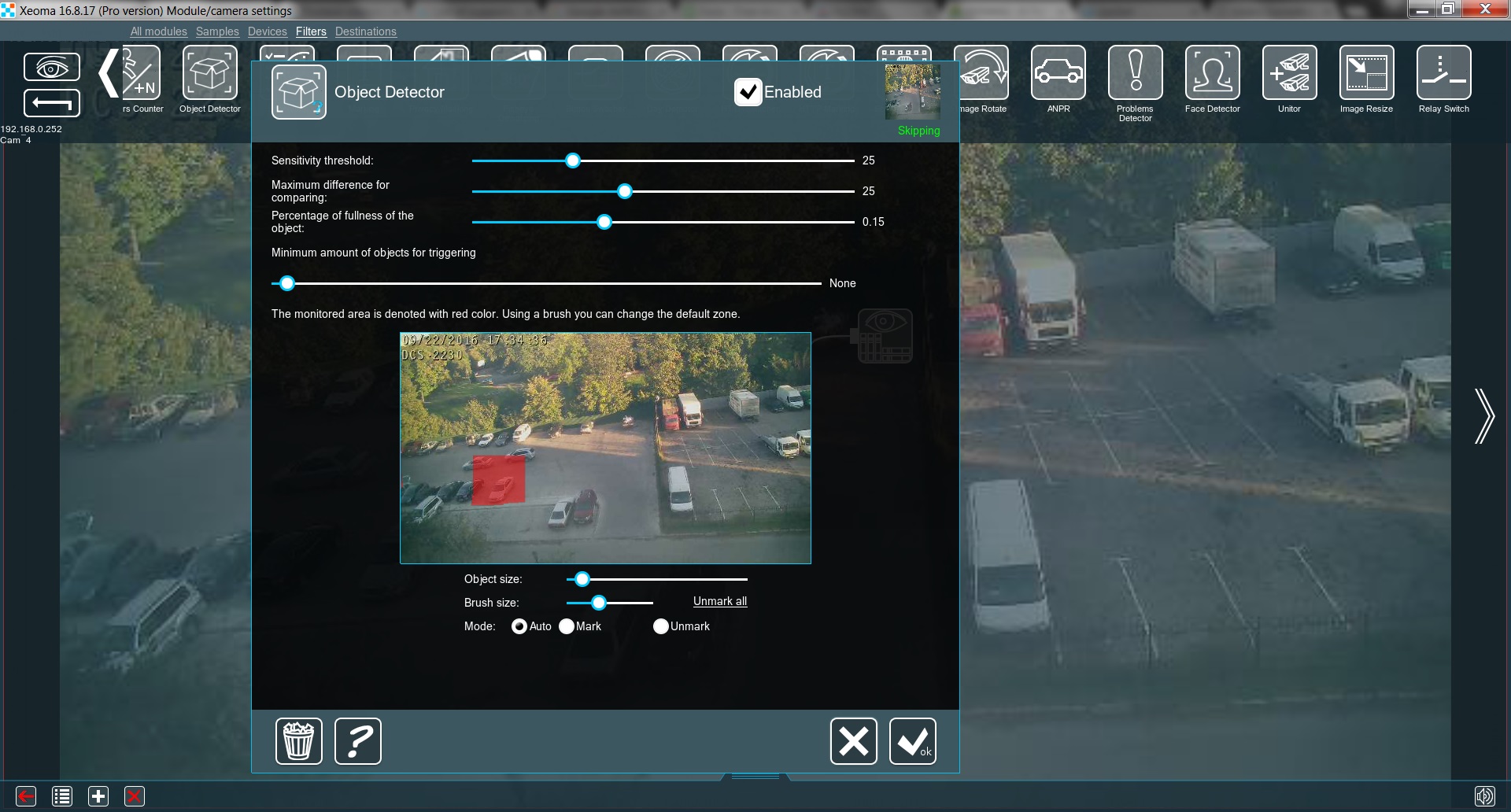
- Finding lost and planted objects. Put the “Object Detector” in the chain. Choose an area for monitoring (e.g. parking lot) by coloring it with the Brush tool. Adjust the sensitivity threshold, the minimum amount of objects for triggering and accuracy to optimize the module’s work. Connect it to the “Preview and archive” module, so that what cameras detect can always be checked in the Archive.
- Bird Recognition. One of the most common causes of technical problems with airplanes is birds crashing into planes and hitting engine turbines during takeoff and landing. It is almost impossible for pilots and operators to track birds and prevent collisions without the help of special equipment. However, thanks to the innovative “Bird Recognition” module in Xeoma, airport managers can automatically track the appearance of birds at the airport site and coordinate the route of the aircraft according to the information received.
Add “Bird Recognition” to the chain and connect the notification modules so that the program can inform operators about the presence of birds in the surveillance camera’s field of view.
To avoid false positives, add the “Motion Detector” module before the “Bird Recognition” module. In its settings, use the Brush tool to select the area where no birds should appear.
- Emotion Recognition. One of the most important aspects in the airport is security. However, it is almost impossible to keep an eye on a huge number of people at the same time. With the help of the intelligent module “Emotion Recognition“, security staff can easily identify aggressive-minded people, as well as those who behave suspiciously: overly nervous and so on.
When a camera captures a person’s face, it transmits the data to Xeoma, after which the module analyzes it and determines the emotions the person is feeling. The program can notify airport staff about certain detected emotions, for example, only aggression. If the operators are in doubt, they can send a security guard to check the person.
As you can see, Xeoma’s functionality allows to tackle all of these problems with ease.
7 October 2016
Read also:
Counter-Terrorism With Video Surveillance


