Loitering Detector


Consider another example: an otherwise unremarkable individual is watching your front door intently for quite some time and never goes too far from it. A tourist trying to find their way through an unfamiliar street block? Or a stalker? Or, perhaps, a burglar waiting for you to leave? Either way, this is something you’d rather not overlook and take precautions.
Examples like these are numerous and, sadly, not uncommon nowadays. Loitering may not be grounds for arrest but is certainly a cause for suspicion. Until recently the only eye that could take note of this kind of behavior was a human one. However, the ever-watchful eye of a camera is learning from its creators and starting to keep up with them. Automation options are a key factor for any modern security system, as cameras and computers with software are incapable of negligence. Let’s see if Xeoma can take up the guard’s duty.
“Loitering Detector” is another partner for “Object Detector” (the first being “Cross-Line Detector”), so the common chain should look like this:
“Object Detector” looks for objects (preferably moving ones) on the live feed, assigns them unique IDs and sends this data to “Loitering Detector”. The latter counts the time those objects spend within the frame and triggers when they take too long:
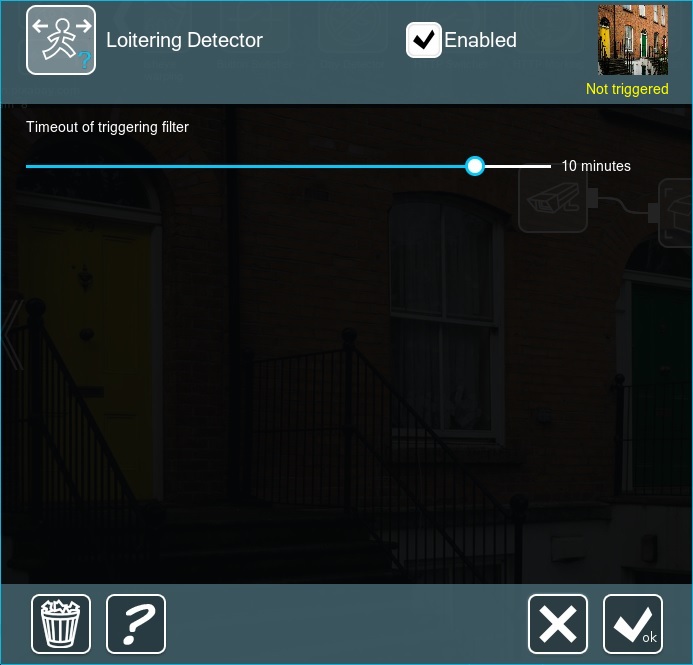
Note that the module in need of fine-tuning is “Object Detector”, as it decides what to count as an object. Now let’s see if we can apply this system to the examples above and identify loitering with intent. First, a restricted zone – a chain like this should provide tight security:
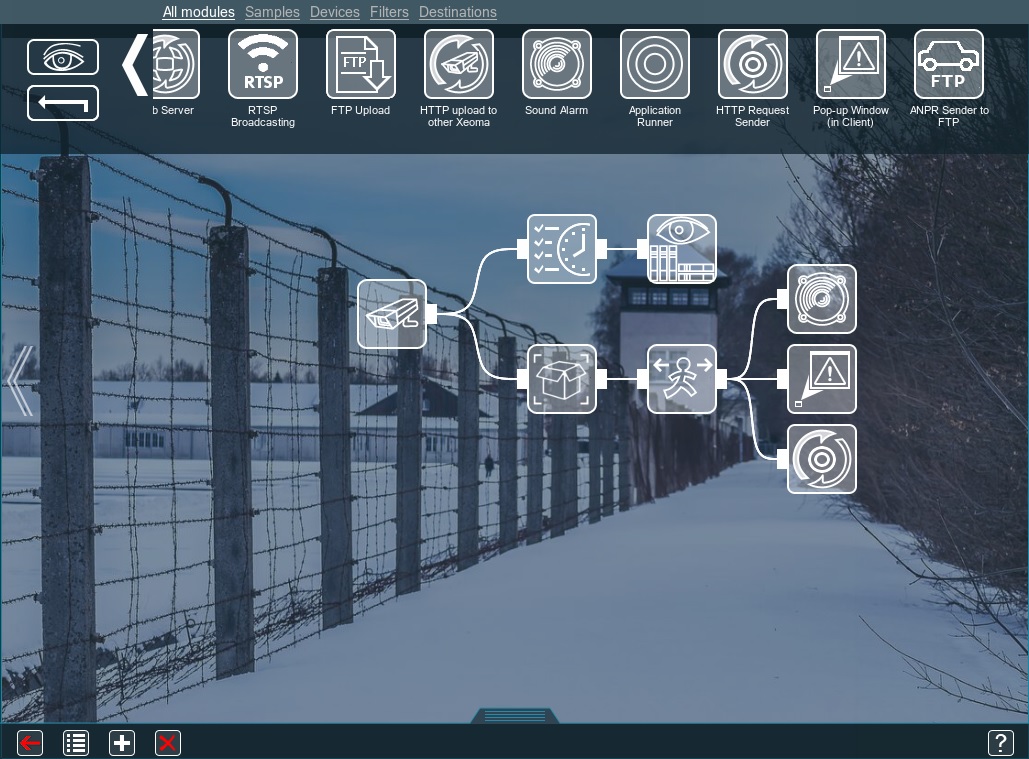
Since this is a restricted access facility, we assume the archive is needed only for specific hours – hence the “Scheduler”. Once the timer in “Loitering Detector” reaches the limit, it triggers a “Sound Alarm”, makes a “Pop-up Window” and “HTTP Request Sender” informs some external device (e.g. centralized logging system for further analysis). If needed, you can add “Detector of abandoned objects” to the chain as well – to trigger a separate alarm. This will back up the guards on duty in case something escapes their attention.
On to the front door – here is a useful chain for it:

Xeoma archives the footage 24/7, since you wouldn’t want to leave your property unwatched. Later you can simply fast-forward through the video while viewing the archive. Once “Loitering Detector” has something to report, it will trigger “SMS Sending” to instantly notify you. The second line of defense is “Face Detector” – it will count the faces in the frame and when it exceeds a certain limit (e.g. 4), it will send you an SMS as well: there is a commotion near your door that you should be aware of, be it harmless or loitering with intent. You can add “Sending Email” to the chain, if you’d like to get a picture or a video of the event – it will attach the necessary information to the message. This way you should be able to tell if any suspicious behavior is present.
If you are looking for a more contemporary reaction, Xeoma can also send push notifications to your phone (with the “Mobile Notifications” module) or send a message to a Telegram messenger (with the “Telegram Bot Notifications” module), both available in Xeoma Standard edition as well as Xeoma Pro.
Do you want to not only protect your business from intruders, but also make it prosperous? Xeoma has 8 ways to grow your business fast!
Video content analysis as a science has made an impressive leap forward this decade, finding new efficient ways to make software recognize patterns. The next exciting step would be object recognition and identification.
Try Xeoma for free! Enter your name and your email to send the license to in the fields below, and click the ‘Get Xeoma free demo licenses to email’ button.
We urge you to refrain from using emails that contain personal data, and from sending us personal data in any other way. If you still do, by submitting this form, you confirm your consent to processing of your personal data
Created: December, 14 2017. Last updated: February 2, 2026
Read also:
Slip and Fall detector
Visitors Counter
Face Detection and Recognition
Security at railway stations